Accessing a remote SSH server typically involves the use of the PasswordAuthentication method, which relies on a combination of username and password. This approach is suitable for a majority of users, as it is a prevalent authentication technique for SSH and other systems.
However, there may be instances when manual authentication is not ideal, and a passwordless login becomes preferable or even necessary. This is particularly true for system administrators who frequently access SSH servers and execute automated commands on remote machines. To achieve this, you can configure and utilize public-key authentication for automatic SSH server login without providing your username and password.
You can automatically log in to an SSH server without entering your username and password by configuring and using the public-key authentication method.
Related: How to copy files remotely using SSH
Related: How to execute remote SSH commands in the background
Steps to enable passwordless login in SSH:
- Open your terminal application.
- Generate an SSH key pair on your local host if you haven't already.
$ ssh-keygen Generating public/private rsa key pair. Enter file in which to save the key (/home/user/.ssh/id_rsa): Enter passphrase (empty for no passphrase): Enter same passphrase again: Your identification has been saved in /home/user/.ssh/id_rsa. Your public key has been saved in /home/user/.ssh/id_rsa.pub. ##### snipped
Make sure to not set any passphrase for the key pair
Related: How to generate SSH key pairs
- Ensure PubkeyAuthentication is enabled on the remote SSH server.
$ sudo grep PubkeyAuthentication /etc/ssh/sshd_config [sudo] password for user: PubkeyAuthentication yes
Public key authentication is normally enabled by default.
- Transfer your SSH public key from the local host to the SSH server.
$ ssh-copy-id user@remote-host /usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed /usr/bin/ssh-copy-id: INFO: 2 key(s) remain to be installed -- if you are prompted now it is to install the new keys user@remote-host's password: Number of key(s) added: 2 Now try logging into the machine, with: "ssh 'user@remote-host'" and check to make sure that only the key(s) you wanted were added.
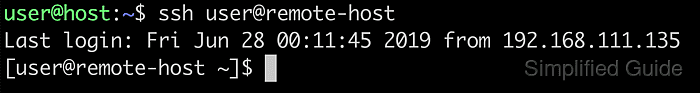
- Test the configuration by logging in to the remote server.
$ ssh user@remote-host Last login: Fri Jun 28 00:12:15 2019 from 192.168.111.135 [user@remote-host ~]$
You will no longer be prompted for a password when logging in to the server.

Mohd Shakir Zakaria is an experienced cloud architect with a strong development and open-source advocacy background. He boasts multiple certifications in AWS, Red Hat, VMware, ITIL, and Linux, underscoring his expertise in cloud architecture and system administration.
Comment anonymously. Login not required.
